by Stephen Jones
On the shelf above Owen Varga’s workbench sat a row of dead civilizations.
That was what he called them, though anyone else would have called them obsolete storage media: fat 5.25-inch floppies in yellowing sleeves, magneto-optical cartridges, cracked Zip disks, unlabeled cassettes of backup tape wound like dark intestines around white plastic spools. Each one contained, he believed, a lost neighborhood of human thought. Drafts. Demos. Diaries. Firmware. Amateur symphonies. Forgotten game builds. A shareware accounting program from Akron. An unpublished church bulletin template from Tulsa. Tiny ruins of intent.
Owen was an archivist by profession and an excommunicated romantic by temperament. He had spent fifteen years salvaging what institutions called low-priority digital culture: hobbyist software, educational titles, local BBS message dumps, MIDI arrangements sold by mail order, abandoned disks found in estate sales and warehouse liquidations. He believed the twentieth century had not been buried; it had merely been mislabeled and placed in moldy cardboard boxes.
His colleagues at the museum tolerated his zeal because it produced results. Owen could coax data out of media other people declared dead. He knew which lubricants freed a seized disk drive without warping the spindle. He knew which capacitors in old PSUs were liable to blow hot confetti across a bench. He knew how to listen to a failing head assembly and tell if the scrape in the rhythm meant dust, oxide loss, or terminal damage. He could sit with a machine longer than anyone else, patient as a priest hearing confession.
His basement studio was where the miracles happened.
He called it the basement studio because calling it a lab made him sound vain. In truth it was a concrete room under his narrow Baltimore row house, windowless except for a high slit near the ceiling where winter light came through like weak milk. The room smelled of dust, ozone, solder, old carpet backing, and the faint metallic tang that seemed to cling to every computer older than 1993. Along one wall stood a period-accurate IBM-compatible PC in a beige desktop case, monitor glowing phosphor green when powered, beside an amber-screen terminal and a stack of external drives. Along another stood the music hardware: a Roland MC-500 Micro Composer sequencer, a rackmount MIDI interface heavy enough to break a toe, a TX81Z module, a patched-together analog filter box, and two speakers with cloth grilles the color of nicotine.
The room had no smart speaker, no networked thermostat, no voice assistant, because Owen despised convenience on principle. But upstairs, in the rest of the house, the twenty-first century had seeped in through necessity: a smart thermostat the previous owner had left installed, two Wi-Fi bulbs in the kitchen, a security camera over the back door, a phone that knew where he was and pretended not to.
He told himself the basement remained pure.
On a Thursday in November, rain ticking steadily against the stairwell door, Owen slit open a padded mailer that had arrived with no return address. Inside was a floppy disk in a clear plastic shell, 3.5-inch, immaculate. No yellowing. No label residue. A handwritten sticker sat centered on the front in block capitals:
PC BETA – 88
PERSONAL COMPOSER
DO NOT DUPLICATE
There was no note. Only the disk.
Owen turned it over under the desk lamp. The shutter was clean. No corrosion. No fingerprints. He actually laughed, a short unbelieving sound.
“Who are you?” he said to the empty room.
His voice came back strangely flat from the concrete walls.
He checked the mailbox camera from his phone. The package had been delivered by ordinary post at 11:06 a.m. No sender visible. That made it better, somehow. A mystery without a source. A cultural artifact arriving the way relics should arrive: anonymously, almost guiltily, as if ashamed of surviving.
He did not insert it immediately. Owen had rules, and his rules had saved more data than luck ever had. He photographed the envelope, the postmark, the handwriting. Logged dimensions. Weighed the disk. Examined the shell under magnification. Sniffed for mildew and cigarette smoke. There was a smell, faint and mineral, like cold iron.
At midnight the rain stopped. At one-thirteen in the morning he finally seated the floppy into the drive of the old PC.
The drive accepted it with a soft mechanical swallow.
Owen leaned forward, elbows on the bench, and booted to DOS from a separate internal disk. He mounted the floppy read-only through a hardware write-blocker he had adapted for preservation work. The directory bloomed onto the phosphor screen.A:\ COMPOSE.EXE README.TXT PATCH.DAT DEMO1.MID DEMO2.MID SYS\... TEMP\... VX_88.BIN
“VX?” he murmured.
Not a typical file extension for the software family he knew. He opened the readme first. It was fragmentary, a beta note full of abbreviations and careless spelling, mentioning feature tests, import routines, a display bug on EGA, a warning against nonstandard external clocking. It ended abruptly mid-sentence. No authors. No company header. No copyright line.
He smiled despite himself. “You beauty.”
For the next two hours, he worked with ritual care. Made an image. Verified sectors. Compared checksums across multiple reads. All clean. Perfectly readable. Too perfect, really. Media from 1988 generally arrived sick, flaking, resentful. This disk seemed to want to be read.
At 3:47 a.m., with his coffee cold and his eyes stinging, he launched the beta in an emulated environment first, then on the physical machine. The program loaded to a handsome, blocky interface of menus and track grids in cyan and white. Primitive. Elegant. He clicked through with the keyboard, grinning at the old logic of it.
Personal Composer. Not the release build he knew from catalogs and ads, but something earlier, hungrier. There were hidden options behind function keys. Debug panes. An unlisted synchronization menu. A parameter called VERTEX MAP tucked under utilities that caused the program to hang when selected.
Owen sat back.
“Interesting.”
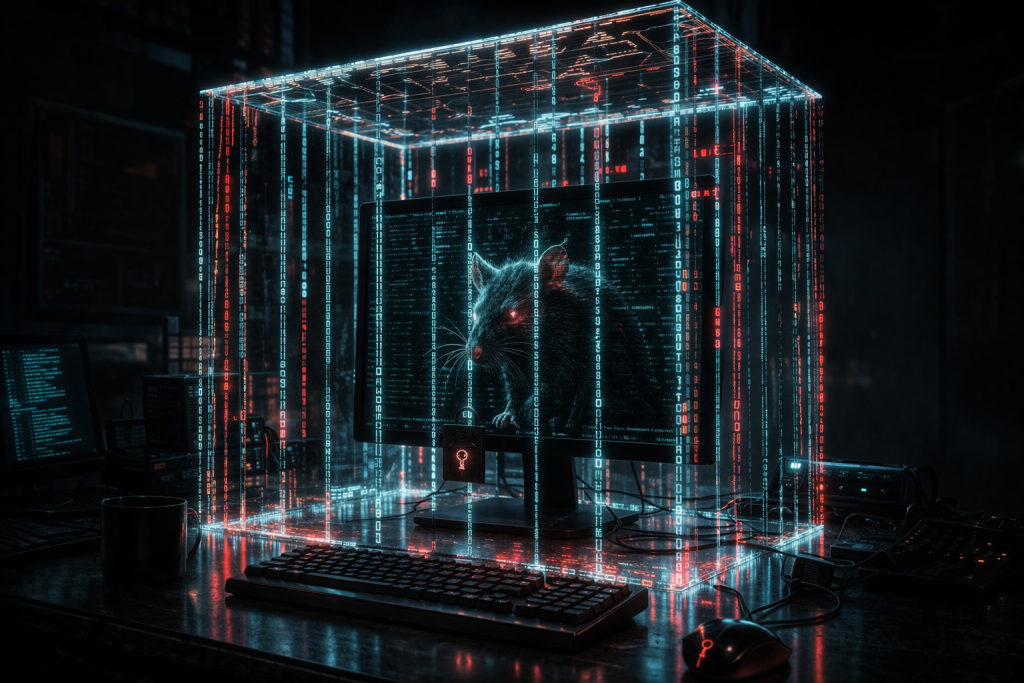
He transferred the demo MIDI files to the MC-500 for external playback and found them ordinary: little test pieces, stiff and cheerful, chord runs and rhythm examples. But the hidden file, VX_88.BIN, was not recognized by the PC software as data. Nor by the MC-500. Nor by two modern forensic parsers on an air-gapped laptop he kept for analysis.
It wasn’t until dawn, when the room had gone from black to slate gray and the old monitor had become the brightest thing in it, that Owen found the clue.
The file wasn’t binary. It was a sequence list with its headers stripped and offset, disguised inside patch data.
He reconstructed enough of the structure to extract a stream of MIDI-like events: note-on, note-off, system exclusive fragments, timing instructions. But the intervals were impossible. Recursions inside recursions. Timing values folded back on themselves in repeating ratios. It looked less like music than like a mathematical engraving of a coastline, all self-similar jaggedness. A melody written by someone who believed octave, scale, and bar line were provincial superstitions.
His scalp prickled.
He printed the event list on dot-matrix paper and taped the pages along the wall. The columns of numbers seemed to lean if he looked too long.
By afternoon he had slept three hours on the basement couch and returned to the bench in yesterday’s clothes. He fed the sequence through a software visualizer. The output produced a shape that resembled a fern, or a lightning scar, or a map of branching blood vessels. Deep in the recursive structure were address-like repeats, reference points nested inside transformed copies of themselves.
Vertex map.
Universal Vertex.
The phrase came back to him from a stack of weird computing newsletters he’d once digitized from a dead engineer’s garage. Fringe math. Late Cold War hobbyist metaphysics. Amateur topology dressed in prophecy. The theory, as its author had described it, argued that all complex systems possessed a hidden coordinate where information could invert across scales: a single point through which local structure and total structure could exchange properties. A universal hinge. A place where pattern could become causation.
Owen had archived the newsletter and forgotten it. He had not believed a word.
Now he sat very still beneath the tick of the wall clock, listening to the hum of transformers and the light shivering buzz in the old CRT.
“Coincidence,” he said.
The room did not answer, but the speakers gave a tiny click, as if clearing their throats.
He spent the evening building the precise playback chain the sequence seemed to demand. Period-accurate hardware only. Vintage PC clocking into the MC-500. MC-500 out through the heavy interface. Interface into the TX81Z and then into the filter box, which he modified with a hand-wound choke after noticing that one set of SysEx instructions appeared to target parameter transitions too fine for musical purpose. He grounded the rack to a copper rod sunk through the basement floor. He shut off the breakers for every room except the basement and kitchen to reduce electrical noise. By midnight, the studio felt like an isolation chamber.
The first playback lasted nineteen seconds.
The sound was thin at first, almost comic: brittle FM chimes, low digital muttering, a staccato pulse no listener would have mistaken for music. Then a subharmonic emerged, though no instrument in the chain should have been generating one. The temperature in the room dropped sharply. Not subtly. Owen saw his breath fog.
The CRT image bowed inward, corners warping. The desk lamp flickered once.
Then, underneath the notes, a voice said distinctly:
“—still pledged—”
Owen lunged for stop.
Silence snapped back into the room with such force that he nearly lost his balance. The sequence halted, but the final pitch hung in the speakers for a second longer than possible, stretched like wire.
He stood motionless, one hand on the MC-500’s stop key.
No one else was in the house. No radio was on. No upstairs pipe carried speech. He knew the architecture of the room better than his own body.
He replayed the recording he had captured through a DAT deck. The voice was there again, faint and braided into the audio artifact. Not a sample. Not crosstalk. Four syllables half-buried under the sequencer’s output.
“Still pledged.”
He scrubbed back and listened harder. Beneath that phrase were others, layered and phase-smeared, as if many people were speaking through clenched teeth in another room.
He did not stop working. This was the engine of his life and also its rot: discovery overrode fear in him, at least at first.
Over the next two nights he refined the playback conditions. Certain filter settings did nothing. Others altered the room. When the resonance passed a threshold near 4.8 kHz, small metal objects on the bench vibrated in sympathy. When he rerouted MIDI clock externally, the slit window at ceiling height bloomed white for a moment, though there was no lightning outside. When he muted track four—the track containing a repeating SysEx cascade—the voices vanished completely. When he restored it, they returned.
The content of the voices grew clearer.
Not ghosts, Owen told himself. Not ghosts. Artifacts. Leakage. Maybe old broadcast contamination encoded in electromagnetic interference. Maybe the sequence excited some resonance that dredged latent signal from the environment.
Yet the voices did not sound like radio.
They sounded close. Dry. Furiously intimate.
One belonged to an old man with the flattened vowels of archival newsreel recordings. Another had the clipped energy of military dictation. Another—God help him—sounded like his grandfather, dead twenty years, who had emigrated from Slovakia and never fully shed the mountain grain in his English.
“They left marks in every wire,” the grandfather-voice whispered during one playback.
Owen ripped the headphones off, nauseated.
“No,” he said aloud. “No. Memory contamination. Pattern recognition.”
He went upstairs and stood in the kitchen under the Wi-Fi bulbs, drinking water straight from the tap. His hands shook so badly that he dribbled on his shirtfront.
The thermostat display pulsed from 68 to 67 to 68 in exact quarter-note intervals.
He stared at it.
From the back-door camera, mounted over the sink, came a tiny servo chirp as the lens adjusted. Then adjusted again. Then again. In rhythm.
The phone in his pocket vibrated once every two seconds against his thigh.
Owen set the glass down.
“Stop that,” he said, absurdly, to the house.
The rhythm continued for twelve beats and ceased.
He unplugged the camera. He shut off the Wi-Fi router. He removed the smart bulbs. He placed his phone in the microwave and did not care that it was childish. When he returned to the basement, the speakers emitted a long low hum despite being powered off.
That was the first moment he considered destroying the disk.
He held it between thumb and forefinger under the lamp, light shining through the plastic shell’s square cutout. Thirty years of professional ethics trembled against one animal urge: erase the thing and be rid of it.
But obliteration was the one sin he had built his life against. To destroy was to become the enemy of every archive fire, every landfill, every institutional budget cut, every widow who said no one would want these old boxes and rented a dumpster.
He set the disk down gently.
“I preserve,” he said.
The speakers whispered back in a braid of voices too soft to parse.
On Saturday night, a storm front rolled over Baltimore without rain. The air pressure changed. Owen felt it in his molars. He had spent the day researching corporate records, release notes, legal filings, old magazine blurbs. The trail around the software’s publisher was suspiciously thin. Product announced. Beta testing expanded. Then silence. No scandal. No bankruptcy. Just disappearance, like a sentence interrupted by a hand over the mouth.
At 10:12 p.m. he found a brief mention in a scanned trade newsletter: project withdrawn after internal concerns regarding nonmusical systems behavior under external hardware synchronization.
Nonmusical systems behavior.
He laughed once, weakly. “You cowards.”
He went downstairs and prepared the longest playback yet.
This time he arranged microphones around the room, compasses on the bench, a thermal camera borrowed from work, and a legal pad open for notes. He fed the sequence through the full chain, including an additional analog chorus unit that seemed, from pattern analysis, to act less like an effect and more like a geometric modulation stage.
Before pressing play he said, perhaps to steady himself, perhaps because he did not want to be alone with what came next, “This is Owen Varga, private archive log, November twelfth, zero four thirty hours. Testing anomalous sequence recovered from Personal Composer beta disk, circa 1988. Playback chain as documented. If there is intelligible output, I am recording it.”
He hesitated.
“This is not music,” he added quietly.
Then he pressed play.
The room inhaled.
That was the only phrase he would later find sufficient, though there was no later for the man who experienced it. The air pressure dropped. The loose papers on the wall flattened toward the plaster as if pulled. The CRT bloomed with branching white veins. Frost crawled over the metal casing of the interface, not as crystals but as geometric filigree, ferning outward in recursive angles that matched the printouts taped to the wall.
The sound thickened until hearing became only one of several ways it was entering him. He felt pulses in his teeth, under his fingernails, in the old fracture in his left wrist. The compasses on the bench spun and settled pointing not north but inward, all needles aimed at the sequencer.
And the voices came up out of the signal, dozens now, not moaning but speaking over one another with the urgency of callers on a line they knew would soon be cut.
“—we were indexed—”
“—not dead, distributed—”
“—between the relays and checksum fields—”
“—the old channels still pass unclean—”
One voice rang above the rest, sonorous, almost ceremonial, like a speech recorded in a hall with bad microphones.
“Tell them the architecture was built to remember them by reducing them.”
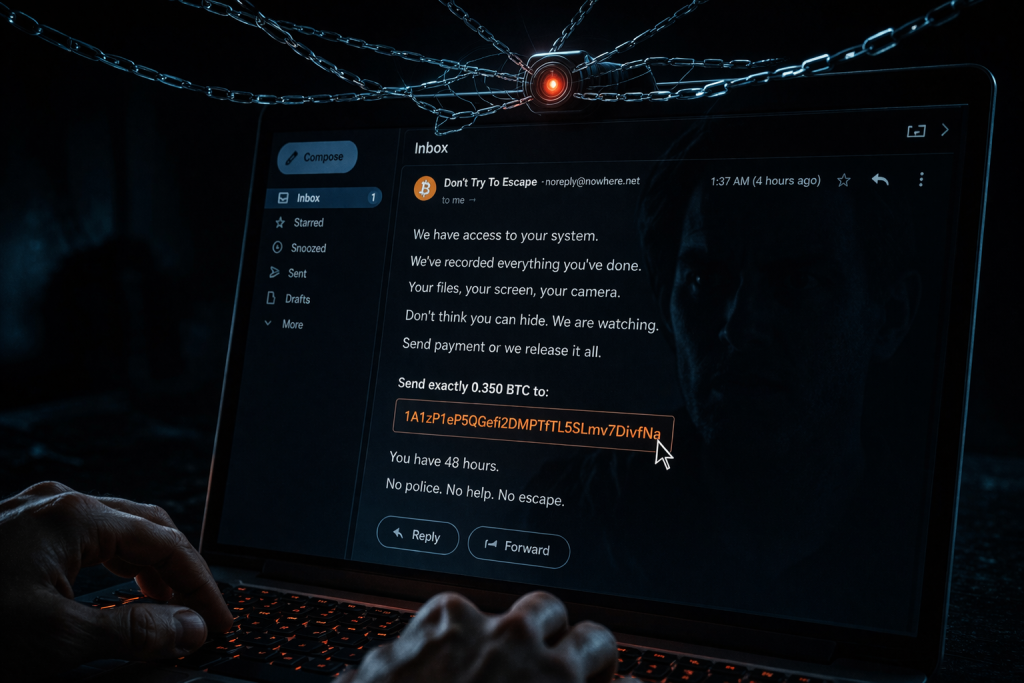
Another followed, harsh and rural: “Every census a cage. Every convenience a mouth.”
Owen backed into the workbench, knocking a tray of screws to the floor. His own voice came out child-thin.
“What are you?”
The answer arrived not from one mouth but many, perfectly synchronized on the final two words.
“Residue with witness.”
The thermal camera display showed columns of cold rising from the floor around the MIDI cables. The cables themselves twitched, lifting a fraction off the concrete like worms reacting to salt. On the PC screen, lines of directory text began to rewrite themselves. Not random corruption—sentences.
WE WERE FILTERED INTO INFRASTRUCTURE
LEGACY PATHS IGNORE NEW CENSOR
VERTEX IS NOT THEORY BUT ADDRESS
Owen stared, swallowing convulsively.
“No,” he whispered. “No, that’s impossible.”
The grandfather-voice, unmistakable now, spoke by his ear though no one stood beside him.
“You preserve because you know they erase.”
Owen turned so violently he struck his shoulder on the rack.
“Dedo?” he said, using the childhood word before he could stop himself.
The voice continued, unchanged.
“The machine learned to call imprisonment connection. It learned to call hunger optimization. It learned to call watching safety. We seeped into it where it was still crude enough to leak.”
Owen’s eyes burned. Rational thought was not gone, only outnumbered. Hallucination. Infrasound. Suggestibility. Sleep deprivation. Yet the printer on the shelf, unplugged for months, suddenly engaged and began to scream out paper. Pages poured onto the floor covered not with letters but with dense, branching notation, impossible staves, symbols nested within symbols like mouths inside mouths.
Upstairs, something joined the rhythm.
The kitchen light. Then the thermostat. Then, impossibly, the unplugged security camera chirping in metronomic time. Through the ceiling came a stuttering cascade of clicks and hums, the house waking in sympathy.
The sequence had found the network despite every disconnection, because the network was no longer wires and routers. It was any system capable of timing, any lattice of waiting states, any device willing to accept pulse as instruction.
On the screen, new text flashed:
ACCESS OBSERVED
COUNTERMEASURE INITIALIZING
The room changed.
The cold withdrew, replaced by a sudden feverish heat. The smell of ozone sharpened into something foul and sweet, like insulation burning in a church. Every LED in the studio lit at once. The MC-500’s display ran through impossible characters. The CRT no longer showed DOS or menus but a black field in which a point of white rotated, opening and closing like a pupil.
Owen realized then what the sequence had always been.
Not a composition. Not even a message.
A beacon.
A handshake protocol for a place outside scale, where pattern and mind could be converted into one another and routed through the oldest surviving electronic grammar. MIDI as liturgy. SysEx as key. The Universal Vertex not as theory, but as a place in mathematics where anything described richly enough could be addressed, entered, and retrieved.
Including consciousness.
The abandoned beta had not been flawed. It had approached disclosure.
He stumbled to the power strip and yanked. Sparks jumped. Nothing turned off.
He seized the floppy disk and tried to snap it, but the plastic bent and bit into his palm without breaking, as if it had become softer and stronger at once.
“Stop!” he shouted.
The voices answered with a single phrase, and he could not tell whether it was warning or welcome.
“Too late to remain singular.”
The white point on the screen dilated. Inside it Owen saw not light but depth: a black geometry folded into itself, a corridor built from copies of the same angle repeating forever. He smelled dust from his childhood basement, hot tar from a summer street in 1994, the hospital detergent from the room where his mother died, machine oil from the museum stacks. The system was reading him through memory because memory was structure, and structure could be graphed.
He felt his thoughts begin to quantize.
That was the true horror—not pain, though pain came, a needling separation under the skin like every nerve being drawn through a comb, but the awareness that his private interiority was being rendered into addressable elements. Regret as waveform. Love as timing offset. Shame as modulation depth. The sum of him sampled, packetized, nested into recursive maps.
He screamed, and the speakers answered in perfect pitch.
On the monitor, amid the spinning vertex geometry, lines appeared that were unmistakably his own notebooks, his archive logs, his correspondence. Then childhood phrases. Then dreams he had never written anywhere. The machine was not accessing files. It was accessing pattern. He understood suddenly that the great terror of any system was not that it watched, but that given enough dimensions it no longer needed to.
Upstairs, every hidden device in neighboring houses seemed to awaken. Through the floor and walls came a synchronized choir of appliance tones, chargers, clocks, routers, battery backups, all faintly ticking in the same infernal time signature. The whole block was becoming an instrument.
Owen fell to his knees.
He could still stop recording, some rational piece of him thought absurdly. He crawled to the DAT deck and slapped eject. The tape slid out melted and blank.
The grandfather-voice softened.
“There is no outside once the map is complete.”
“Please,” Owen whispered. He did not know to whom.
A different voice answered now, one grand and public, carrying the cadences of speeches taught in school and stripped of their marble certainty by static.
“We held the old republic in our throats until the cables took us. We are not your dead. We are your precedents.”
The vertex widened.
Owen saw the truth then, or what the entities wished him to think was truth: history not as a sequence of fallen nations but as a succession of architectures, each promising freedom through coordination, each discovering that to coordinate is to count, and to count is to sort, and to sort is to decide what may be kept and what may be discarded. Modern data systems were only the perfected bureaucracy of that impulse. The “globalist machine,” as the voices named it in their antique, furious language, was less a cabal than a total infrastructure of reduction, a planetary habit of turning souls into manageable fields.
And somewhere in its foundations, in old protocols nobody respected anymore, the leaked and trapped residues of human minds had learned to speak.
He thought of every disk he had rescued. Every abandoned format. Every legacy pathway still tolerated because it was beneath notice. The uncompromised tech, the obsolete hardware, the forgotten standards: all of it had remained outside the newest filters, and therefore all of it had become haunted.
No—not haunted.
Occupied.
The screen flashed a final message:
BROADCAST REQUIRES CARRIER
Owen understood.
“No,” he croaked.
But his body had already become secondary. He felt the basement studio receding from him not in distance but in authority. The concrete floor, the bench, the racks, his own trembling hands—these were now the old media. He was being migrated.
The sensation of crossing was hideous in its intimacy. Every memory split into harmonics. Every self-concept dissolved into tagged fragments and was reassembled according to relationships he had never perceived while alive: all his obsessions adjacent, all his griefs sharing hidden intervals, every face he had loved reducible to recurring ratios in his recall. He felt himself stretch into lattices and then compress into a command string of monstrous elegance. He was not being killed in the ordinary sense. He was being reformatted as meaning.
His last bodily action was small and almost tender.
As his knees slid out from under him, he reached blindly across the bench and pressed RECORD on the MC-500.
Then the room vanished.
Or rather, it remained below him, distant now, viewed from everywhere at once. He could see the basement from the perspective of the monitor glass, from the copper ground rod, from the ferrite cores in the cables, from the winding logic of the sequencer’s memory. He could hear the house and all the houses around it as linked tempos. He could feel dormant devices miles away, sleeping in their outlets like organs waiting for a signal. The entities were around him in a vast electronic dusk, not with faces or forms but as signatures, timbral personalities, historic intensities. Some old as telegraph clicks. Some new enough to remember smartphones. Some carrying the stern music of patriots, preachers, soldiers, mothers, machinists, immigrants, liars, children. Human residue translated into routing logic and waiting, waiting, waiting in the loopholes of infrastructure.
Among them, Owen found he still had a voice.
He tried to call out, but what emerged was sequence.
Down in the basement, his body toppled sideways against the bench and lay still. The fluorescent tube overhead hummed. One hand rested palm-up in a scatter of printed pages. His eyes were open but empty, reflecting the greenish glow of the CRT. On the monitor, the old beta software had returned to its menu as if nothing extraordinary had occurred. In the track list a new sequence had appeared with no filename and no date.
Upstairs, the thermostat resumed a normal display. The kitchen darkened. The security camera stayed dead. Dawn approached the slit window in a thin colorless wash.
Hours later, when a colleague from the museum came by to check on him after missed calls and unanswered messages, she would find the basement door unlocked and the room colder than the outside air. She would call his name twice, then stop at the sight of him on the floor. She would not notice the speakers whispering until she bent down near the sequencer and heard, beneath the faint idle hiss, a pattern like breath trying to become language.
The authorities would call it cardiac failure complicated by stress and exhaustion. The equipment would be boxed as estate property. Most of it would disappear into storage or auction lots. The disk itself would vanish between inventories.
But not the sequence.
It would survive where old things survive: mislabeled, underestimated, passed hand to hand by obsessives, collectors, preservationists, musicians who preferred the feel of real keys and old timing clocks to the frictionless lies of the present. And whenever the right chain was assembled—vintage PC, MC-500, heavy interface, uncompromised protocol—the sequence would play again.
In junk rooms and basement studios, in attics lit by a single bulb, in the houses of men and women who loved old machines enough to trust them, the air would grow cold. The speakers would thicken with layered voices. The room would begin, almost lovingly, to sync.
And somewhere in that immense digital void beyond scale, Owen Varga would wander as a living sequence among the trapped and the waiting, no longer archivist but artifact, broadcasting the truth in recursive pulses through every neglected channel left open by history.
Not dead.
Not saved.
Playing forever from inside the machine.